Common Cloud Misconfigurations That Lead to Data Breaches
Most cloud security incidents do not involve sophisticated hacking techniques. Instead, they are caused by simple misconfigurations that leave systems exposed to the internet. Understanding these common mistakes is the first step toward preventing costly data breaches.
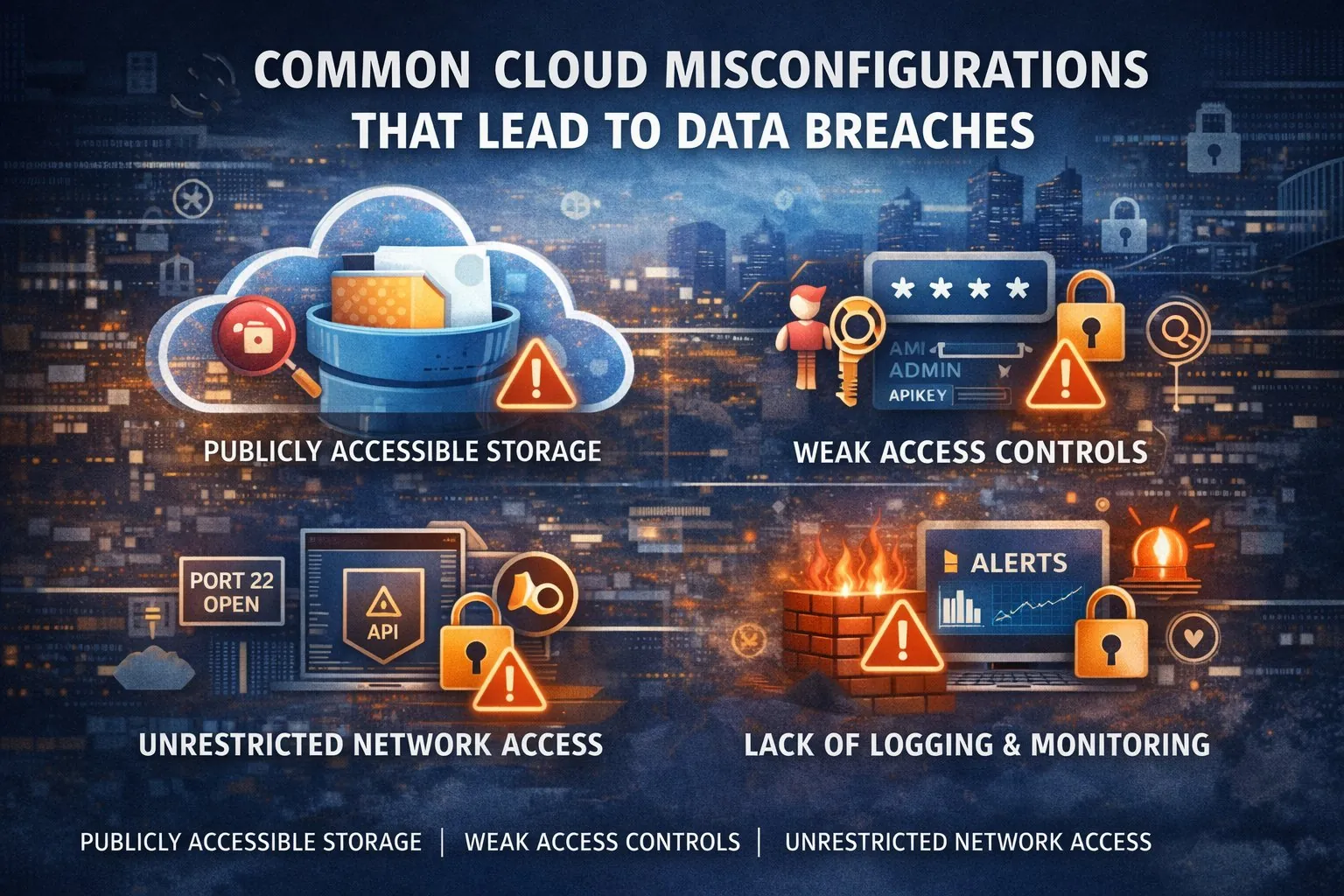
One of the most frequent issues is publicly accessible storage. Cloud storage services are designed to make data sharing easy, but a single misconfigured permission can expose sensitive files to the world. Many organizations discover such exposures only after data has already been indexed by search engines or accessed by unauthorized users.
Another major risk area is identity and access management. Overly permissive roles, unused accounts, and lack of multi-factor authentication significantly increase attack surfaces. Granting broad administrative access “for convenience” often violates the principle of least privilege and creates unnecessary risk.
Unrestricted network access is another common problem. Open management ports, exposed APIs, and lack of network segmentation make it easier for attackers to move laterally once they gain access. Cloud-native firewall and network security tools are powerful, but they must be correctly configured to be effective.
Logging and monitoring gaps also contribute to delayed breach detection. Many organizations enable logging but do not actively review alerts or analyze logs. Without proper monitoring, suspicious activity can go unnoticed for weeks or even months, increasing the impact of an attack.
Finally, lack of governance across multiple cloud accounts or subscriptions leads to inconsistent security posture. Different teams deploying resources independently often results in fragmented controls, unmanaged assets, and security blind spots.
Preventing these issues requires a combination of automation, policy enforcement, and regular security reviews. Cloud security posture management tools, infrastructure-as-code practices, and periodic audits help identify and remediate misconfigurations early.
Cloud environments are dynamic by nature. Continuous visibility and proactive controls are essential to ensure that convenience does not come at the cost of security.

